 “Conclusions –This study makes the case that two activities of targeting disbelieved by most of the public and ridiculed in the media and by law enforcement not only take place but also are proliferating at an alarming degree: (1) the transmission of voices by remote to auditory targets, who are the only ones to hear those voices, and (2) the reading of minds by remote methods. It also shows that the attackers use similar tactics in employing the voices.” –“Auditory Targets: A study of Synthetic Telepathy, or V2K, An Aspect of Electronic Targeting (October, 2018)”
“Conclusions –This study makes the case that two activities of targeting disbelieved by most of the public and ridiculed in the media and by law enforcement not only take place but also are proliferating at an alarming degree: (1) the transmission of voices by remote to auditory targets, who are the only ones to hear those voices, and (2) the reading of minds by remote methods. It also shows that the attackers use similar tactics in employing the voices.” –“Auditory Targets: A study of Synthetic Telepathy, or V2K, An Aspect of Electronic Targeting (October, 2018)”
This is the second time to post “Auditory Targets: a Study of Synthetic Telepathy, or V2K…” from 11-2018. Cannot get the study out of my mind. Night and day since have thought of how reading it has totally affected life for the better. First off, realize God sees us all. People are not alone. And TI’s ARE NOT ALONE in any of the heinous ways they are tortured daily 24/7. Second, understand that the study is so thorough and conclusive in its investigation that it should be read in it’s entirety.
Below is the study for everyone to read with a few sentences removed. All 45 pages of truth about what is happening to millions of US citizens today and millions more around the globe- are reprinted below… (My comments appear in italics in green highlight.) Put highlights in black of important items in text of study.
If anyone doubts the study below, just ready New York Times- Marshall Sella’s, “The Sound of Things to Come,” from March 23, 2003. About directed energy weapons devices being mass produced by the millions for the Department of Defense. Or read psychiatrist Dr. Colin Ross’s 2006, “The CIA Doctors: Human Rights Violations by American Psychiatrists.” Or read, Paul Brodeur’s 1977, “Zapping of America: Microwaves, Their Deadly Risk, and the Cover Up.” -These two books especially support every torture done to the targeted individuals below.
Government agencies in Missouri, especially Springfield fire department and Springfield, MO police department might want to read this study and the NYTs article and two books mentioned above to familiarize themselves with what happens to US citizens who are targeted with microwave, radio wave, acoustic and radar weapons? (Beside the US citizens in the news working in Cuba, China and Russia that are or have been US diplomats also attacked with directed energy weapons.)
AUDITORY TARGETS: A STUDY OF SYNTHETIC TELEPATHY, OR V2K, An Aspect of Electronic Targeting (October, 2018)
Executive Summary
Too little is known about the voices that many people claim that they receive. Those voices are transmitted by remote methods, and only the people to whom they are aimed hear them. The persons receiving the voices are known as auditory targets. This study attempts to broaden the knowledge of the reader concerning the phenomenon of the voices and at the same time dispel some of the beliefs that many doubters hold about those voices.
Targeting and Targets
This is an in-depth study of the voices, often known as V2K, which is one aspect of electronic targeting. However, to understand the voices, one must also understand the concept of targeting. If some organization or group dislikes someone, if they wish to do harm to that person, and if they have the means to do so, that person becomes red-lined, or targeted.
The process of attack is called targeting, the end result of which is expected to be the neutralization of the victims. Neutralization can mean totally isolating the targets, sending them to mental institutions or prisons, or causing their eventual deaths. We refer to the people behind the targeting as the attackers, or perpetrators, and the victims of the attacks as targets, “targeted individuals,” or simply TIs.
An increasing number of Americans report that they are being attacked by unidentified remote sources using unknown devices or methods to produce many harmful physical and neurological effects. Previous studies show that the number of targets has increased considerably since the early 2000s. Thus, targeting appears to be proliferating.
Critics of people who claim to be targeted often suggest that the targets are instead victims of mass hysteria; however, they fail to describe an event that could lead targets to mass hysteria that would not also affect the entire American population. Several thousand targets living in diverse locations who complain of many of the same remote-delivered results are not likely to be victims of mass hysteria. In fact, our experience shows that targets have already been suffering from those effects before they begin researching and communicating with other targets on the web.
Targeting takes several forms: (1) One form employs yet highly classified devices that can focus and fix upon a person to pound him with many physical effects. (2) Another form of targeting consists of using similar devices to focus and fix upon a person to achieve a myriad of neurological, or psychological effects. (3) Still another form concentrates on harassing the target on-site in various manners: using organized stalkers against him; vandalizing his property; making surreptitious entries into his domicile; tampering with his postal mail, his computer, and his telephone; strewing rumors about him in his neighborhood and work place, and employing other forms of harassment.
The first two forms operate by remote methods, which means that the attackers’ device or devices do not touch the body, and the two forms can also operate in tandem with each other. The remote distance can be only meters away from the target or hundreds, perhaps thousands of miles away. The farthest range has not yet been determined by targets. The third form is performed on the ground in or near a target’s surroundings. The voices are used only in the first two forms of targeting. A target can receive only one of the three forms of targeting or all three forms simultaneously.
Voice Transmissions
One of the most sinister capabilities of the attackers is transmitting voices into the heads of targets by remote methods that only the targets can hear. We refer to those persons who receive the voices as “auditory targets.” Those targets become involuntary hearers of those voices, and there is no known way to prevent the voices from being heard. Victims have come to call those voices a variety of names, such as voice-to-skull (V2K), microwave hearing, microwave auditory effect, electronic telepathy, synthetic telepathy, audio subliminal messages, and the Voice of God.
In addition to transmitting voices, the attackers can also mimic and project many other sounds into the domiciles of the victims and into their surroundings, for example, sounds of doors slamming, birds cooing (when there are no birds), dogs barking (when there are no dogs), unexplained thuds against the wall, telephones ringing, doorbells chiming, loud popping noises, people shouting, and many other sounds. We do not yet know whether in every case persons other than the auditory targets can hear those sounds, as the sounds normally occur when the targets are alone.
The Auditory Targets
Persons who state that they hear voices are routinely considered by law enforcement and others as psychotic. In fact, authorities often require that the auditory targets submit to “psychiatric evaluations,” claiming that the victims are likely to hurt themselves or others. Psychiatrists, citing the DSM, invariably label the auditory targets schizophrenic or paranoid- schizophrenic. Some auditory targets are even committed to mental institutions based on those evaluations.
Indeed, psychiatrists have a vested interest in condemning those who hear voices as paranoid-schizophrenics, for psychiatrists can treat only natural symptoms, not induced or remotely transmitted ones. Thus, to protect the credibility of their profession, psychiatrists must necessarily disclaim the possibility of actual transmitted voices, or synthetic telepathy.
An article in the January 1, 2018? Issue of The Washington Post by Nathaniel Morris called “This Secret Experiment Tricked Psychiatrists into Diagnosing Sane People as Having Schizophrenia” drove home the point that psychiatrists cannot accurately diagnose schizophrenia. Morris related an experiment conducted by Dr.David Rosenhan of Stanford University, which sent eight perfectly sane people to different hospitals claiming that they heard voices.
One of the participants was a psychiatrist and three, psychologists. All eight “patients” were admitted to the respective hospitals’ psychiatric wards where they said that they no longer heard the voices. Despite that, they remained from seven to fifty-two days. While there, they were given a total of 2,000 pills, among them antipsychotics and antidepressants, most of which they secretly discarded. Even the nurses who attended the patients often noted actions on the part of the patients that suggested that they were mentally ill.
When the experiment was revealed, Morris writes that the experiment became a “disaster” and an “albatross” for the psychiatric community. Dr. Rosenhan stated that the experiment proved that “. . . we cannot distinguish the sane from the insane . . . .”
Victims of remote voice transmissions cover the entire spectra of the American population. They include both genders and all ages. They also include all races, ethnicities, levels of education, professions/occupations, religions, philosophies, states of health, political leanings, economic statuses, social strata, and life styles. Many of the victims are veterans.
Auditory targets range from the very young to the very old, the minimally-educated to the MDs and PhDs, from the atheistic or agnostic to the piously religious, from the recipient of public assistance to the well off, from the apolitical to the political activists, and from single people of various life styles to the family-focused patriarchs and matriarchs. The only known commonality that links the victims is that they all receive the voices.
The victims state that they hear the voices and other V2K-related sounds wherever they go whether they are in airplanes at high elevations, in hotels and other places outside their domiciles, in heavily wooded areas, in underground facilities, and wherever else they go. Thus, we know that the remote voice-transmitting devices must have the capability of going through walls and other structures and being beamed over vast distances.
V2K doubters point to the presence of the voices heard everywhere as proof that the auditory targets are truly mentally ill. However, the remote-driven V2K was publically demonstrated in 1973, forty-five years ago, and it is virtually certain that in the meantime far more sophisticated but classified methods have been developed.
In previous studies of the voices, the earliest remote auditory targets state that they began hearing the voices in the very early 1980s. Some targets hear the voices only sporadically while others receive incessant voices both day and night. Auditory targets are found in every industrialized nation and in many developing countries. Our study focuses only on Americans.
Until recently, targets in general, including the auditory targets, have been treated with doubt and disdain by the media, law enforcement, and the public, who consider their claims incredulous. However, in the late summer of 2017, attacks on US diplomatic personnel in Havana, first called “sonic” in the media reports, focused international attention on some of the symptoms that targets receive, for example, tinnitus, loss of hearing, visual and balance problems, and vibrations, all oft-mentioned effects of targeting. Later, diplomats in Uzbekistan and China also complained of similar effects.
More recent reporting on the symptoms of the diplomats hints that some of the victims may have also heard voices. A New York Times article entitled “Update—NYT: Microwave Weapons Are Prime Suspect in Ills of U. S. Embassy Workers,” dated September 1, 2018, states that the method used on the diplomats could transmit “loud booms” and “words.” If indeed the diplomats heard voices, US Government entities and the American media have seemingly downplayed that information.
The Remote Voices
A study of the patents suggests that the attackers do not use one single device on their targets but probably several different devices. One or more devices will probably administer the physical effects on targets, and another device or devices will deliver the neurological, or psychological effects. We still do not know how contact is first made with the targets and how that contact can be fixed upon the targets permanently. Nor do we know for certain the methods of delivery of both the physical and the neurological effects.
The voices are a key element in neurological, or psychological attacks on targets that lend toward mind control. Without the voices, the attackers can only harass the targets physically. If the aim of the attackers is only to make the lives of the targets uncomfortable and painful, the physical attacks achieve that purpose. Indeed, some targets receive only the physical effects of targeting.
If the attackers seek to take over the lives of their targets, they must also take over the minds of those targets, thus the neurological element of the attack plan. Without the voices both to the targets’ heads (audible) and to the targets’ subconscious (inaudible), mind control would be impossible.
Proof of Remote Delivered Voices
One of the main objectives of targeting, including the voices, appears to be mind control. Mind control represents a major feature of neurological warfare. The United States, among other industrialized nations, has shown a keen interest in neurological warfare, including the projection of sounds and voices, since the 1940s. In 1961, Allan H. Frey described the possibility of producing voices by remote in an article called “Human Auditory System Response to Modulated Electromagnetic Energy” published in the Journal of Applied Physiology.
Not until 1973, however, did researcher Joseph C. Sharp successfully demonstrate the actual transmission of remote voices into the skull. Dr. Don R. Justesen, Director of Laboratories of Experimental Neuropsychology at Veterans Administration Hospital in Kansas City, described that method in an article called “Microwaves and Behavior” in the March 1975 issue of the American Psychologist. It seems that Justesen had gotten his information directly from Sharp, who was by then conducting a secret study called Pandora for the US Navy, a study that also involved the voices.
Justesen explained that by “radiating themselves with ‘voice modulated’ microwaves, experimenters could distinguish clearly nine words sent to them by remote. He wrote that article in 1975. By 1997, the method of sending voices to peoples’ head by remote had been perfected, as evidenced in an announcement on the Environmental Protection Agency web site in that year. Describing the Department of Defense’s voice research, the announcement stated that the “innovative and revolutionary technology . . . offers a low-probability-of-intercept radiofrequency (RF) communications, [the feasibility of which] has been established using both a low intensity laboratory system and a high power RF transmitter.”
By the early 2000s, the capability of sending voices by remote to people’s heads without their knowledge or consent was a hard and fast fact. An article in The Washington Post in January 2007 revealed that “In 2002, the Air Force Research Laboratory patented precisely such a technology using microwaves to send words into someone’s head.”
Representatives of the laboratory involved refused to discuss both the reported patent as well as any research related to it, adding, “We can only stress again that the world media avoid publishing the full scale of the progress in the research of the remote control of human nervous system.” Seemingly the media has since cooperated with that request, as the media today usually states or suggests that when people are reported to hear voices they are mentally ill.
In the last decade and a half, scientists have doubtlessly made improvements to the devices/methods used to communicate remotely with subjects. Although the reality of remote voices to people’s heads can no longer be seriously debated, we still do not know for certain the devices or methods currently used to transmit the voices from the sender to the receiver. Just as in the last fifteen or so years the development of methods for using DNA has been greatly improved, we believe that likewise the development of voice transmission devices and methods has made giant leaps.
How Remote Voices are Transmitted
One method of transmitting the voices by remote is called “silent sound,” described in Dr. Oliver Lowery’s Patent Number 5,159,703. Silent sound, or the present-day subliminal sound, is often conducted over public address systems, and is inaudible to the ears but subconsciously perceptible. That method has been adequately demonstrated over the years.
The patent states that by using supercomputers, attackers can “analyze human emotional EEG patterns and replicate them, then store these “emotion signature clusters” on another computer and, at either real-time or at will, ‘silently induce and change the emotional state in a human being’.” In other words, silent sound can be used for mind control.
A similar method is known as Audio Spotlight, which is projected in the range of above 15,000 Hz, which humans cannot hear, to achieve the same effect. Auditory targets will either hear nothing or will experience a type of continual tinnitus. Audio Spotlight can be conducted directly to the victim using air type transducers, directly to the victim’s brain using “modulated microwave pulse train,” or by imposing messages on top of commercial radio or television transmissions. We still do not know the range of the Audio Spotlight; however, it has been heard at 200 meters when used in quiet environments.
Many similar patents attest to the interest in communicating between humans by remote methods, including the following: US6470214 (1992), O’Loughlin/Loree, “Method and Device for Implementing the Radio Frequency Hearing Effect (microware hearing); US6052336 (1998), Lowery, “Apparatus and Method of Broadcasting Audible Sound Using Ultrasonic Sound as a Carrier (ultrasound); and US6587729 (2002), O’Loughlin/Loree, “Apparatus for Audibly Communicating Speech Using the Radio Frequency Hearing Effect (microwave hearing). Those methods have been demonstrated and proven effective.
Many targets believe that the attackers use hypnosis to entrain the auditory target’s subconscious to comprehend—but not hear–the content of those inaudible voices.
Indeed, hypnosis is often used. In 1974, researcher J. F. Schapitz corroborated that belief when he stated, “In this investigation [,] it will be shown that the spoken word of hypnotist may also be conveyed by modulated electromagnetic energy directly into the subconscious parts of the human brain – i. e. without employing any technical devices for receiving or transcoding the messages and without the person exposed to such influence having a chance to control the information input consciously.” In other words, the victim is entirely helpless to reject those thoughts conveyed to his subconscious.
Because the method of delivery is performed remotely, attackers are able to assault the victims with the voices 24/7 with complete impunity. As the devices/methods are still largely unknown and unseen, victims are left with no known universal defense against the voices. Unlike a TV or a radio, the remote voices cannot be turned off. Victims of the voices must endure them day and night, day in and day out.
The Study
A group of auditory targets set out in 2018 to study the phenomenon of voice hearing by using credible published material, including declassified government documents, descriptions and demonstrations of patents, their own experiences and those of other voice-hearers, and logic and reasoning. Such is the nature of V2K that probably only voice-hearers themselves can understand its complexities and conduct an accurate study of its many aspects. The objective of the study was to provide a complete picture of the voices.
In the study, we usually refer to the synthetic voices as voice-to-skull, or V2K, a derivation of the term V2S that was first used by the US Army. In the interest of brevity and uniformity, we shall use the all-inclusive term V2K for the voices. However, V2K is actually somewhat of a misnomer, as it refers only to the transmission of the voices to the victims. In other words, V2K is a one-way transmission from the attackers to the voice hearers.
Nevertheless, many auditory targets have learned that they can respond to the voices using only thought, or telepathy, thus producing two-way transmissions. When we use the term V2K in this study, we mean that the attackers can speak to the victims using some type of synthetic telepathy, and, likewise, the victims can speak to the attackers via the same method.
Although V2K is only one aspect of targeting in general and although targets receive other projected remote sounds than the voices, this study deals with only the remotely transmitted voices sensed within the targets’ skulls. We include other aspects of targeting only in their relation to the synthetic voices.
Certain constraints complicate this research project: (1) Although V2K is known to have existed for about a half century, little is known about how it has been used, as much of its usage has apparently been conducted in secrecy. (2) Many inventions fall under the cover of national security and are thus unpatented and probably highly classified. (3) Very little has been objectively and authoritatively written about V2K since its demonstration in 1973.
(4) Auditory targets have been consistently labeled mentally disturbed by the US Government, the medical community, especially psychiatrists, and the mainstream media, making credibility a factor. 5) Terminology also presents a problem. Different victims use different terms to explain the sources, conditions, and effects of the voices. (6) Only a small group of auditory targets participated in this study.
Not withstanding those several constraints, as far as we are aware, this study represents the first attempt to perform a comprehensive study of V2K. The objective of the study is to reveal all that is known about the voices. The result of the study is expected to be helpful to the victims themselves, many of whom are still grappling with the consequences of the voices, and also as a tool for educating the public about remotely delivered voices and their effects on the victims.
Unfortunately, due to still too little verifiable scientific knowledge about the various current devices and methods surrounding the voices, the study was unable to answer authoritatively all of the questions concerning the voices. Nevertheless, in the absence of hard proof, we have presented plausible explanations about all known aspects of the voices based on the knowledge at our disposal and our experiences. The validation or the disproving of our views awaits the exposure of still-secret technical knowledge and devices not yet known by the public.
Despite still unanswered questions concerning voice hearing, the burden of proof appears to rest upon those critics who claim that voices cannot be transmitted into the heads of victims. They must disprove that remotely transmitting voices is possible. There is more than adequate proof, which we shall present further in this study, that the voices can and are being remotely transmitted to unwilling and sometimes unknowing recipients.
Conventional Non-Remote Voices
Our study pertains to only the remotely delivered voices. One should not confuse the remotely delivered voices with the voices that use on-the-body devices. Several devices have been invented that allow a hearing-impaired person to hear non-remote voices. The Cochlear is one of those devices.
Invented in 1985, the cochlear is a very small device implanted in the ear that allows hearing-impaired persons to hear sounds that do not go through the hearing canal. Instead, the device bypasses the auditory nerve to transmit sound directly to the brain. A device that resembles a hearing aid is worn on the outside of the ear that serves as a sound processor.
More recently, several inventors have developed hearing methods based on Morse code, which is decoded into text and then into speech. Then, there are many types of “hearing aids,” small devices that fit behind the ear that are familiar to all readers.
How the Inaudible Voices Are Used
Of the two types of remote voices, the inaudible, or subconscious voices are by far the more dangerous. The subconscious voices are a main element in attackers’ attempts to achieve mind control. A target’s subconscious receives the voices without the target realizing it, and the target often believes and reacts to those hidden voices. The inaudible voices take many forms, and their uses are almost limitless. Here are some of them.
— Giving victims negative commands. Their commands are often very oblique and subtle, for example: “If I were you, I’d . . . .” or “I think that you should . . . .” or “Why don’t you . . . .” Attackers will also often use politeness instead of terse commands to achieve their effect. Thus, instead of simply saying, “go to sleep,” they will say, “Please go to sleep.” Or they often say, “I’d appreciate it if you would go to sleep.”
— Causing false memories. The power of suggestion to the brain’s subconscious is truly amazing. The attackers condition targets for mind control by inducing “dreams” in which the victims play out whatever role the attackers assign him. One target recounts that while he slept the attackers caused him to believe that he was an elderly Confederate veteran of the Civil War reminiscing about his experiences in the battle of Gettysburg. He was telling his grandchildren about his horse being shot and going down, about his being wounded, and about seeing comrades blown to bits with cannon balls. He woke from the induced dream with real tears in his eyes.
— Making statements about the victims’ family members and friends intended to cause estrangement in relations between them and the victims and thus isolate the victim.
— Causing targets to appear delusional. Usually family members believe that a target is delusional when he talks about the effects of his targeting. If they do believe that their relative is being harassed, they are placed in a very difficult position. If they support the target, they perhaps put themselves and their family in danger of also being attacked. If they do not support the loved one, they are effectively isolating that individual from his family support system on which people have always relied.
— Making victims think in negative terms about almost everybody and everything.
— Blanking out certain thoughts. The attackers’ inaudible voices can not only cause targets to think about the topics that they project into targets’ minds but also cause targets to fail to think about important matters. The attackers appear to delight in making targets forget appointments with people, leave items behind that they intended to take with them, and forget where they place common household items.
The attackers also apparently enjoy causing targets to remember people whose names the attackers have blanked out of the targets’ minds. After the target tries hard for several minutes to remember the name, the attackers will suddenly allow the target to remember that name. This creates a psychological dependency on the attackers for information.
— Making threats to do harm. Attackers will often fill victims’ minds with thoughts that they are, for example, going to burn down their houses, going to cause loved ones accidents, going to send “the death squad,” or going to cause organ failures.
— Creating in victims a lack of confidence in themselves by disparaging their capabilities and accentuating their faults.
— Sending victims on wild goose chases and believing things that are not true. Attackers sometimes convince targets that surveillance bugs are hidden throughout their houses, causing targets to search frantically for those bugs.
— Convincing targets that they have psychic or special powers. One auditory target states that the attackers convinced him that he was able to determine the locations of implanted devices on other targets. He even informed some of those targets where their devices were located.
— Causing targets to believe that they are going crazy. Indeed, because of the attackers’ efforts, many victims do develop faux paranoia and do things that make them seem psychotic.
— Inducing anxiety by filling victims’ mind with lewd and vile stories about friends and loved ones.
— Extracting information about others. For example, the attackers will cause a target to think of people he knows named Joe. Then they will ask, “Joe who?” The target tells the attackers Joe’s surname. Afterward, the attackers query the victim about that individual.
— Getting the target to trust them. One victim tells about perceiving a subliminal voice urging him to trust the attackers.
— Causing targets to see holographic images. Most targets who receive the voices also complain that they often see holographic depictions. One target believes that the attackers insert the holographic images by telling the target’s subconscious what he is supposed to be seeing. The target then draws upon his knowledge and experience to embellish and visualize that occurrence, creating the holographic images. In other words, that target believes that the holographic images stem from his own brain.
— Urging a target to commit suicide. Many targets feel that they are being led to take their own lives. An auditory target who somehow has developed the ability to hear some of the subliminal voices states that he has heard what sounds like a loop-play tape telling him to commit suicide.
Recording the Voices
As far as we know, a method has not been invented that is available to the public that will record the voices that only auditory targets can hear. Some auditory targets have attempted to record the voices but failed to record them in their entirety. However, several auditory targets have reported that they had succeeded in recording certain words and phrases contained in the voices transmitted to them.
The technique used was for the auditory targets to record their surroundings in silence when there were no extraneous noises. Then, the tapes were given to second parties who played the tapes using an audio enhancer of some type. Those persons heard various words and phrases. Probably not every person with technical knowledge could succeed in capturing the voices. The person using that technique must not only have very good hearing but also possess considerable intuitiveness to be able to discern those words and phrases.
What the Voices Tell Us
Auditory targets have neglected for years to analyze the actual voices (V2K) that many of them receive to learn more about the attackers behind those voices. Two different groups of auditory targets studied the voices in 2012 and 2017, respectively, to see whether there were identifiable similar patterns among the attackers. Although the objective of the studies was to examine only what the attackers say in their voices to targets and how they say it, we also hoped that we would get some clues about the nature of the attackers themselves.
A study of this type has inherent weaknesses: (1) The study groups consist of only a small number of targets who receive the voices. (2) There is no standard terminology used in targeting; thus, some participants may have interpreted the questions differently. (3) There is no way to determine whether targets who claim to be targets are true victims, mentally impaired, or perhaps feigning their symptoms to interfere with the study—those persons are often called perpetrators, or perps. (4) The targets’ answers are subjective, based on their own experiences and beliefs. (5) The survey may not ask the right questions.
The 2012 Study
In July-August, 2012, nine auditory targets studied what the attackers say and how they say it. The group hoped that the study would show a pattern in the tactics that the attackers use. To a large extent, the result shows that it did.
Of the nine participants, seven were female and two were male, ranging in age from the thirties to the seventies. Participants represented the South (4), Southwest (3), Mid-West (1), and the Pacific Northwest (1). Seven of the nine targets were Caucasian. Although the number of the participants was small, the targets were relatively representative of the targeted population in gender, location, age, and race. A similar study using the same questions but with different targets, hopefully in different areas, will be conducted in the future to validate or revise the initial findings.
The lives and backgrounds of the targets who receive the voices are diverse, and those targets share very few commonalities among themselves. That suggests that various groups engage in the attacks, not one single group. Each of those attack groups may identify and attack more than one target and thus will have a cadre of technically trained attackers. Also, each group must be large and powerful enough to provide the manpower and finances to sustain the attacks.
About the Attackers Themselves
The purpose of the study was to study the tactics of the attackers, not the attackers themselves. Nevertheless, the answers of the participants do perhaps tell us something about the attackers. Although we cannot be certain that we are correct due to the deceptiveness of the attackers, here is what the auditory targets’ answers reveal about the attackers.
— In most American cases, the attackers appear to be native-born Americans or at least persons who are either perfectly bi-lingual or whose first language is English. Seven of the participants said that the attackers did not have a noticeable accent. That in itself is not particularly significant, as we know that software programs that can be bought off the shelf allow the users to adopt various accents, including an American accent. However, six participants said that the attackers even use local words and expressions in common usage in their areas.
— Most of the participants also agree that the attackers do not appear to be above average in education and intelligence. Despite the ingenious plan used for the attacks, the actual attackers are probably just plain, ordinary people who one would expect to see on the street every day but who have been trained to use the attack devices.
— All targets state that their attackers use profane language, dirty slang, or curse words. That information and their tactics dealing with degenerate sex disproves the notion that the attackers are religious zealots who are attacking targets for the targets’ beliefs or trying to convert the targets to some form of religion. Indeed, although some radical religious groups would doubtlessly target certain people if they had the means to do so, the actual attackers appear to be sorely lacking in personal religious convictions.
— The attackers do appear to follow some common guidelines set out in perhaps an original master plan of attack. That hints that one or more of the attackers may date back to the development of that plan or were at least trained by one of those earlier individuals. If that is correct, some of the attackers may be in their 60s and even in their 70s or still older.
The attackers appear to follow the same or very similar tactics in carrying out their targeting. We have designated those tactics “general” and “specific.” The following sections deal with those general and specific tactics that the attackers use on auditory targets.
The Attackers’ General Tactics
V2K is a form of neurological assault, which always includes mind reading along with the voices. The voices themselves are complex, for there are audible voices, i.e., the usual V2K, as well as the “inaudible” voices, aimed at the subconscious. The latter are sometimes referred to as “layered” voices, imposed upon the usual V2K and/or underlying the V2K. Unfortunately, very few targets are able to “hear” the “inaudible” voices, which produce far more negative results than the “audible” voices.
Deception runs deep throughout the verbal attacks. Without deception, the voices alone would probably have little effect. The tactics that the attackers use reflect that deception. Everything that the attackers say and do seems to have a purpose. The plan of attack is carefully contrived, and psychology plays a major role in its implementation. The following actions identified in the V2K study demonstrate some general tactics that all or most of the attackers appear to use in their neurological assault.
— Talk in a very low volume that allows targets to hear only snatches of what they say. Eight of the nine targets said “yes.”
— Command the attackers to go somewhere or not to go somewhere. Eight targets answered “yes.”
— Accompany their V2K with strange noises that seemingly come from outside, like a dove cooing or a dog barking (when there is no nearby dog). Eight of the nine targets answered “yes.”
— Attempt to cause sleep deprivation. All nine participants answered “yes.”
— Pretend to extort money from or blackmail the victims. In eight of the nine cases, the attackers pretended to extort money from the targets.
— Tell the victims that they are going to hell or to jail. Eight of the targets report that their attackers tell them that they’re going to hell. Of those eight, four targets state that the attackers also said that they were going to jail.
— Address victims by a code name, nickname, or some other name that the victims do not use. Seven participants say that their attackers use code names, or nicknames, for them.
— Claim to be or suggest that they are various groups. All but one participant stated that the attackers have suggested that they represent various groups.
— Give the victims commands when they know that the victims are going to do that action anyway (washing your hands, brushing your teeth, closing the door, turning out the lights, etc.), All nine targets answered “yes.”
— Repeat particular numbers to victims. Seven targets answered “yes.”
— Praise the targets for something that they do or think, a form of “good cop/bad cop.” Seven targets answered that the attackers sometimes praised them; eight targets stated that they played “good cop/bad cop.”
— Use other voices that victims believe that they are not supposed to hear underlying or superimposed over the usual V2K. Most of the participants sometimes hear those additional voices.
— Cause the victims to …have accidents, or ruin something that they are doing. All nine participants answered “yes.”
— Make innuendos about why the targets were selected for targeting. Eight participants said that the attackers made innuendos about the reasons.
— Give the victims specific instructions about what to do or not to do or what to think and what not to think. All nine participants answered “yes.”
— Invite the victims to join them. Eight of the participants were asked to join the attackers.
— Use obvious recordings interspersed in their real-time talking (although those recordings may be in the same voice). All nine participants agreed.
— Tell victims that they are “hardheaded” or “stubborn.” Eight targets said “yes.”
— Suggest to victims that if they do a certain act or think in a certain way that their attacks will stop. Seven targets said at one time or another the attackers hinted that if the targets did as the attackers wished, their attacks would cease.
— Sometimes express anger and frustration. Six targets said “yes.”
— Talk negatively about particular ethnic, political, or religious groups? All nine participants said that the attackers talk negatively about a particular group.
— Pretend that they are religious. In eight of the nine cases, the targets were told that they are going to hell.
— Sometimes hint that they have been assigned to the victims and that the attackers are responsible for them.
— Attempt to take credit for negative things that happen in victims’ lives.
Eight targets answered “yes.”
Letter below placed on porch of home in time for return visit to friends. Had taken dogs to along to run on the four acres friend owns. Attempts to poison them were found outside of a chain link fence during walk on friend’s property. In letter found on porch seven people I do not know wrote notes of sympathy for the death of a dog. Being a targeted individual is to have every aspect of security and safety in your life vanish though repeated harassment, intimidation, remote DEW torture and rape, V2K/BCI, and more.

 Letter left on front porch of TIs home after attempts to murder their dog failed.
Letter left on front porch of TIs home after attempts to murder their dog failed.
The Attackers’ Specific Tactics
Almost everything that the attackers say and do appears to be a part of the attack plan and has an objective. Many of those objectives are obvious in analyzing the answers to the questions. Although we have known those objectives for some time, we have not attempted to determine whether they are commonly used by the attackers. Listed below are some tactics employed by the attackers that our study shows are widely employed to accomplish those objectives.
Cause Anxiety in Targets
Instilling anxiety in targets is a main objective of the attackers. In fact, anxiety is one of their major tools in neutralizing the targets. Anxiety is a horrible condition, as those who have experienced it know very well. For those who have not experienced anxiety, it is a fear of unknown origin, a disquiet that the person cannot fathom. The person is filled with dread, especially at night when the whole world seems to close in upon him. He is like a caged wild animal who seeks an escape, but there is no possible escape. He goes to bed with fear, sleeps fitfully, and wakes up with fear. What better condition could the attackers ask for?
Because of anxiety, some targets eventually commit suicide. Others become psychological basket cases and totally discredited by their fear and the bizarre behavior that it creates. Here are some tactics that the attackers use to induce anxiety in targets.
— Induce dreaming in which they stage frightful scenarios and make the targets the principal actors. Eight of the nine participants said “yes.”
— Call targets ugly names. All nine participants stated that the attackers call them ugly names.
— Try to make targets believe that certain foods and drink(s) and medicines in their domicile have been tampered with? Eight participants said “yes.”
— Comment on and ridicule things that targets write about on the computer. Seven targets said “yes.”
— Instill phobias in targets’ minds (fear of snakes, spiders, germs, water, etc.). Eight of the nine targets answered “yes.”
— Bother targets when they are concentrating on a mental task, such as preparing their income tax returns, etc. All nine targets said that the attackers bothered them while they were concentrating on a particular mental task.
— Suggest that relatives and friends of the victims are also targeted. All nine participants answered “yes.”
— Berate targets about what the targets write or think about and tell them it’s not true. Eight of the nine targets said “yes.”
— Cause “glitches” on the victims’ computer when they do not like what the targets are writing. Eight participants said “yes.”
— Relate to the targets stories about incidents in the targets’ childhoods. All nine participants stated “yes.”
— Criticize victims for something that they said to somebody or thought about somebody and try to make them feel guilty over it. All nine participants answered “yes.”
— Employ code words and expressions such as “hospital” and “emergency room” in their V2K to victims. Eight answered “yes.”
— Lead victims to believe that others are talking about them or making fun of them. Eight targets said “yes.”
— Talk to victims about dead relatives and people whom they once liked very much but are now out of touch with. Seven targets said “yes.”
— Make the victims believe that they knew their families long ago. All nine targets report that their attackers pretend to have known the targets’ families in the past.
— Tell victims that they and their loved ones are going to die. All nine targets answered “yes.”
— Cause one of the voices to sound similar to the victims’ voices. Seven of the nine targets said that the attackers have used or continue to use a voice similar to their own voices.
— Threaten to burn down victims’ houses, destroy their possessions, or vandalize their property. Six of the nine targets answered “yes.” Another target said that they used to but now do not.
— Re-enforce the V2K with holographic images. Eight of the targets experienced holographic images at one point or another in their targeting.
— Mention places on victims’ bodies that are not visible to other people (a scar, a tattoo, etc.)? Six targets said “yes.”
— Try to convince the targets that they are crazy. Eight participants answered “yes.”
— Urge targets to commit suicide. Eight of the nine participants have been or are urged to commit suicide.
— Make targets believe that a person they know said something ugly about them. Eight participants said “yes.”
— Pretend that they can see the targets. All nine participants said “yes.”
— Tell victims that they have a life threatening or a debilitating disease. All participants answered “yes.”
— Project their voices over objects such as the spewing water when victims shower.
Six of the nine targets said that they hear the voices over the running water.
— Increase the physical/neurological torture the night before an important event. All nine participants answered “yes.”
— Sometimes use another language in their voices. Six participants answered “yes,” and five of those said Spanish. One answered that they spoke English but with perhaps a Swedish or Irish accent. Only three of the targets stated that the language used held some significance for them.
— Employ the V2K continually 24/7, using real-time and recorded voices. Seven of the nine participants hear the voices continually.
— Use “inaudible,” or “silent,” voices—sometimes referred to as “layered” voices–to make targets forgetful, e.g., of where they put objects, to take their medicine, to make a necessary phone call, to instill doubt about relatives and friends, and to induce anxiety. All nine targets agreed that the attackers use the “silent” voices on them.
— Blank out the thoughts of targets as well as cause other thoughts to surface in the victims’ minds. All nine targets said “yes.”
— Attempt to convince targets that they are ugly, fat, that they smell bad, or are otherwise undesirable. All nine participants answered “yes.”
— Cause victims to hear actual voices talking about them without the victims seeing the speakers or seeing the speakers’ mouths? (Perhaps the speakers’ backs were toward the targets or the targets could see nobody at all.) Eight of the targets said “yes.”
— Urge targets to eat excessively and eat the wrong kinds of food or perhaps drink too much. All nine targets answered “yes.”
— Often attempt to make the victims believe that they knew the victims at an earlier age, using statements such as “We went to elementary school with you? Or, “We went to high school with you?” Six answered “yes.”
— Relate events in victims’ infancy and childhood to make them feel guilt, remorse, anxiety, etc. Eight participants said “yes.”
— Ridicule and make fun of targets during their prayers. Seven targets said that the attackers make fun of their prayers or their praying. Another target said that they sometimes do.
— Repeat the targets’ thoughts to them as the thoughts come to mind. Eight targets said “yes.” One of those said that the attackers did not repeat them directly following the thoughts but did so later.
— Try to make targets think that they are bad and that the attackers are good. Eight targets answered “yes.”
— Show targets holographic images of Christ and/or other religious figures. Seven targets answered “yes.”
Interrogate the Targets
Although it is easier for the attackers to interrogate the targets at night while they sleep, the attackers also interrogate them when they are awake. The interrogations clearly show the handiwork of psychiatrists and psychologists and the intelligence agencies in devising the plan of attack. The attackers repeat their interrogation questions day after day until they are satisfied with the answers.
Of course, they probably already know the answers to most of the questions, and through mindreading, they complete the information. One of the main objectives in the interrogations is to let the targets know how much the attackers already know about the targets seemingly to frighten them.
— Question/interrogate the targets. All nine targets said that the attackers questioned/interrogated them.
— Tell targets that they are “investigators.” Eight targets answered “yes.”
— Pretend to be local law enforcement or to be working with local law enforcement.
Eight of the nine targets stated that the attackers claimed to be law enforcement or working with law enforcement.
— Try to convince or suggest to targets that they have committed a crime or a sin. Eight targets answered “yes.”
— Show the targets photos of people, places, and objects while questioning them. Eight of the nine participants report that the attackers show them photos and question them about the photos.
— Direct targets’ thoughts to certain people, places, or objects and then question targets about them. Six targets said “yes.”
— State a number, which causes targets to think back when they or their children were that age or to think something else about that number. Seven targets answered “yes.”
— State a particular year and then question targets about that year. Six targets answered “yes.”
— Make targets feel that they have to clarify and articulate carefully their thoughts and even explain them to the attackers? Eight of the participants answered “yes.”
— Cause targets to visualize in their minds the faces of people whom they think of or who the attackers cause them to think of. Eight of the participants said “yes.”
— State a particular first name and cause targets to think of all of the people whom they know by that name. Seven participants said “Yes.”
— Suggest that the targets are not patriotic. Six targets said “yes.”
— Question targets about their ‘relationship” with a particular individual or group.
Seven of the nine targets reported that the attackers questioned them about “relationships.”
— Ask targets questions about places they have lived in or visited. Six of the nine participants said “yes.”
Isolate the Targets
— Tell targets ugly and negative things about their friends and relatives. All nine targets said that the attackers said bad things about their friends and relatives.
— Make targets suspicious of their relatives and neighbors. All nine targets report that the attackers try to make them suspicious of their neighbors.
Induce Dreams
Inducing dreams and staging scenarios are not merely for the attackers’ entertainment. Those dreams and scenarios are undoubtedly intended to induce anxiety, provide additional information about the target’s past (a form of interrogation), and program the target’s thoughts and actions.
— Induce dreaming in which they present a particular theme. Eight participants answered “yes.”
— Cause targets to feel anxious, frightened, or upset as a result of the induced dreams. Seven targets said “yes.”
— Make targets see the other actors in the dreams. Eight targets said that they actually see the other people with whom they are interacting.
Use Physical Effects with Neurological Attacks
— Inflict a variety of physical torture on targets along with the voices. All nine targets receive physical effects.
— Started attacking targets with the physical effects before beginning the voices. Seven said “yes.” Of those, the previous physical effects ranged from 5 minutes to 25 years.
— Cause a ringing in the ears (tinnitus) in targets. Eight of the nine participants report the ear ringing, but one of them said that it occurred about 3.5 years AFTER she started hearing the voices and another one said that it was only “off and on.”
Employ Sexual Themes and Make Sexual Innuendos
— Use expressions such as “(Name of a person) is crazy about you.” and “(Name of a person) wants you.” Seven targets said that at some point in their targeting or very often the attackers use those same expressions.
— Start the V2K during or shortly after targets have relations with or break up with a companion. In six cases, the V2K appears to have something to do with a relationship.
— Attempt to make targets think of (anything taboo) when they are engaged in sexual activity. Seven answered “yes.”
— Touch and manipulate the targets’ genitals through vibrations. All nine targets stated “yes.”
— Use particular trigger words and expressions or show targets holographic images that them feel a sexual arousal? Seven targets said that they are triggered into sexual feelings.
— Attempt to connect targets’ sexual thoughts… through their V2K. Seven said “yes.”
— Refer to targets as being gay or try to make them believe that they are gay, that they are sexually attracted to (anything taboo). All nine participants report that the attackers try to make them think they are gay or to think about having sex with (anything taboo).
End of 2012 Study
The 2017 STUDY
Twenty-two auditory targets volunteered to participate in the second V2K study, 21 Americans and one Canadian whose mother is American born. However, only eleven targets actively took part in the study. The twenty-two intended participants answered twenty questions about themselves and their backgrounds to determine whether they shared any common characteristics. Here are the results.
- The genders of the participants were 15 females and 7 males.
- Racially, there were 18 whites, 1 black, 2 Hispanics, 1 Native American, and no Asians.
- The marital status was as follows: 7 single but 1 with a partner, 11 divorced and 1 separated, and 3 married.
- Age-wise, nobody was under 30, and there were eight who ranged between 30 and 50, twelve between 50 and 70, and 2 over 70.
- Six of the participants had at least one parent who was born in another country.
- Five participants were born in other countries.
- No target was adopted or had himself adopted children.
- Four participants were the only child of their parents.
- Three of the participants were left handed; one was ambidextrous but preferred using the right hand.
- Thirteen participants had abused drugs/alcohol (not including occasionally smoking pot) at some time in their lives.
- Educationally, three did not finish high school (1 of those later got a GED), ten finished high school and attended some college, four obtained BA’s or BS’s, three got master’s degrees, and one became a PhD. One participant did not answer that question.
- In religion, 14 were Christian, 3 were atheists, 3 were agnostics, 1 considered himself a Muslim/agnostic/Christian mystic, and 1 was ambivalent about religion.
- Politically, thirteen of the participants were not political at all and nine either vote or are somehow involved in the political process.
- Ten of the participants earned less than $20,000 a year; seven, from $20,000 to $60,000; and five earn over $60,000.
- The careers of the participants naturally varied: two were in sales; two, in education; two, in real estate; and three were disabled (not determined whether it was related to their targeted). The other participants worked in other undefined areas or were retired.
- Of the 22 participants, four were retired, nine were employed or self-employed, and eight were unemployed or on medical disability or otherwise disabled. One participant did not answer the question.
- No participant had served in the Armed Forces.
- Only five participants had worked on some level of government or with the government in some capacity.
- Seventeen of the 22 participants had reported their targeting to the authorities.
- Thirteen of the 22 participants had undergone medical procedures of one kind or another before discovering their targeting, four had never had any type of surgery, and two had surgery after discovering that they were targeted. The answers of other participants were not clear.
Of the twenty-two intended participants in the second V2K study, only eleven actually answered the questions. They were supposed to answer 250 questions, sent to them in sets of from 10 to 20 questions. Unfortunately, one of the 11 participants did not answer Set 5 and 4 participants did not respond to Set 6. Therefore, the study had to conclude at the fifth set of questions with the answers of only 10 participants. That means that participants answered only about 60 questions, or only about a fourth of the intended questions.
Each set of questions and the answers to those questions are seen following. The reader can judge for himself whether the study reveals any meaningful information about the voices and the attackers.
SET 1
- In what year did you first start hearing the V2K?
1981, 1990, 1995, 1996, 2006, 2010 (2), 2011, 2012, one answer was indefinite but it suggested that the voices began years ago, probably in the 1990s.
[In this sampling of targets who receive the voices, one can see that the earliest date at which the attackers were able to project their voices was 1981. Five participants got the voices in a 17-year period from 1981 to 1998. Five of the targets started getting the voices over only a 6-year period in the 2000s. Thus, it appears that the number of targets increase in the 2000s and increase significantly since 2010. This suggests that as the method becomes more sophisticated, a proliferation of targeting occurs. It may also suggest that the ease of identifying and targeting victims has improved and that the attackers trained to handle victims have increased in number.]
- In what state or country did you first hear the voices?
Illinois, Massachusetts (2), Virginia, California, South Carolina, Colorado, Tennessee, New York (2)
[Six of the locations were in populous western, central, and eastern states. Two of them were in the South. One of them was in the Rocky Mountains. This indicates that targeting occurs all over the United States, perhaps more so in heavily populated areas.]
- Where were you when you first heard the V2K?
Eight participants were in their domicile. One was in a car. And another one was at his work place.
[This indicates that the voices can be projected to any location. The location where the voices begin seems to depend on the timing decided by the particular attackers. In my experience, the attackers choose a time when the targets are most emotionally vulnerable and when the situation is the quietest, which may explain the eight cases when the voices were first heard in the targets’ domiciles.]
- Do you recall what the attackers first said to you?
[The answers were, of course, mixed. However, all of the attackers’ statements were obviously designed to be unsettling, perplexing, and frightful to the targets.]
- How many voices did you at first hear?
[Six participants heard two or more voices. Four participants heard only one voice. Thus, this question is probably not really relevant.]
- Were they male voices or female voices?
Five participants heard only male voices. Four heard a mixture of males and females. One heard only a female voice.
[Thus, we can see that unless the attackers are purposely changing their voices, which they are able to do, male attackers predominate.]
- Did the voices have a particular accent? (If so, please explain.)
Only three participants noted a particular accent. One stated that it was a west coast accent, one a NY accent, and another one, a mid-west one.
[Unless the attackers were purposely disguising their voices, this indicates that the attackers were probably located in the same areas in which the targets heard the voices. However, that still does not indicate what devices/methods the attackers were using.]
- Did the attackers use the same voices every day?
One participant answered that he was unsure. Another participant said that the attackers stated that they were using new voice-sampling software. One said that at first they used the same voices but later started to “garble” the voices. One participants answered “no.” One participant stated that at first they were those of family members and then later, strangers. Another participant said that the voices changed from time to time. Only one participant answered definitely “yes.” One said “not at first.” Still another participant said “sometimes.”
[Thus, this question is probably not meaningful, as we know that the attackers can clone voices of others or otherwise disguise their voices.]
- Are the voices you hear today the same ones that you first heard?
Five participants stated “yes.” One said “no.” One said “sometimes.” One participant wasn’t sure. Another participant stated that the voices stopped when he went on meds. One participant did not answer that question.
[Again, this question is obviously not relevant, as the attackers can change their voices using off-the-shelf computer programs. Whether or not the attackers change their voices seems to depend on the particular attackers.]
- Do you receive the voices only occasionally, during the day, during the night, or continually. (Please explain.)
[Nine participants state that their voices are continuous. Another participant says that he no longer gets the voices. Therefore, once the voices begin, it appears that the objective of the attackers is to inundate the targets with voices continuously.]
SET 2
- Do your attackers pretend to be religious?
Six participants stated “yes.” One said that they did at first but quit after they could not convince him of it. One stated that they mocked religion. Another participant said that the attackers called it a “spiritual awakening” and that he hated blacks and Jews. Only one said “no.”
[It is obvious that the attackers do usually pretend to the targets that they are religious. Most people have some religious leanings. Thus, this is a vulnerable area for targets.]
- If so, what religion do they claim to represent?
Four participants said Christian, but one of those four stated that they also sometimes suggested that they were al Qaeda (Moslem). One said that they are “anti-religion.” Another one said that they were a “Christian coalition” and they sometimes mentioned that they were vegans. A 7th participant answered “all religions,” including Satanism. An 8th participant said that the attackers were “spiritual” but claimed no particular religion. A 9th participant said that they purported to be the opposite of what he believed. A 10th participant had answered “no” concerning the attackers’ use of religion.
[As in Question 1, the attackers attempt to confuse and mislead targets concerning religion and the identity of the attackers. They may either be trying to blame a particular religion or religion in general for the attacks or trying to persuade the targets to accept their version of religion. Attacking one’s beliefs is a way to frustrate targets, cause them anxiety, and damage their self-worth, therefore aiding in isolating them. It may also suggest that the attackers may be left to their own choices about what to claim about religious beliefs.]
- In their talking, do the attackers pretend to identify with a particular political party, civic group, or other organization?
The answers vary. Two participants answered “no.” Two stated “Republican.” One stated that they claimed that they were white supremacists. Another one said that they did not specify a particular party or group but wanted him to know that they were politically knowledgeable. Another participant said they were ignorant of politics and did not even know the governor of the state. One participant said that they claimed to be part of a government program and that they had amnesty. A 9th participant stated that they mostly pretend to be very right wing and lean toward harsh conservative viewpoints. A 10th participant said that they often changed their views but wanted him to believe that they were knowledgeable of politics.
- Do the attackers tell you or suggest that you are going to hell or to jail?
All ten participants say that they have been told that they are going either to jail or to hell.
[Those threats are made to cause targets to think that they are targeted because they did something wrong. This makes the attackers appear justified in assaulting the victims. The threats attempt to induce anxiety in targets. Part of their program appears to be to frighten targets about their future, instill fear, and keep them in a state of waiting for something bad to happen to them because they deserve it.]
- Do the attackers have a particular code name for you?
Four participants answered “no.” Four answered “yes,” of whom two of them did not elaborate on the names. Two participants said that the attackers called them by their first names.
[Whether or not to use a special code name for targets appears to be a decision of the particular attack group.]
- Have the attackers told you or suggested to you who they are?
Only two participants answered “no.” Eight participants stated “yes.”
[Once again, the attackers obviously seek to confuse the targets concerning their identity. This is purposeful. If all of the attackers admitted that they represented a single group, it would allow victims to focus their efforts to identity them.]
- If so, what did they tell or suggest to you?
Only two participants said that their attackers gave them no clues or suggestions about who they were. Three participants stated that the attackers were family members/friends/neighbors/former classmates, in other words, people whom they knew. Two said that the attackers suggested that they represented the government. One participant said that they “were for hire.” A 9th participant said “They have tried to dissuade me from remembering their names from the very beginning.” The 10th answer was not clear.
[It is a well-known fact to most targets that their attackers attempt to turn them against family members, friends, and others. It is also known that the attackers can clone actual voices and use those voices as if they were their own. The attackers know that the best way to alienate and thus isolate targets is by making them believe that neighbors, family members, friends, etc. are behind their attacks.]
- Have the attackers’ ever projected their voices to you through the TV, radio, or other device?
Only one participant stated “no.” The other nine participants heard the V2K through various devices and means.
[The attackers obviously have the capability of projecting sound through familiar instruments/devices, including running water in a shower. They have the capability of directing the sound to almost any location either close to targets or at a distance. That, of course, is designed to awe and frighten targets and make them believe that the attackers are very powerful.]
[It is obvious that the attackers have the capability to blanking out memory, thus making targets forget to do ordinary things.]
- Do the voices sometimes tell you that they are “responsible” for you or that they have been assigned to you?
Five participants answered “yes.” Two participants answered “no.” One said that they used to do so. Two answers were not clear.
[This tactic appears designed to place the blame for targeting on the victims.]
SET 3
- Do you hear the voices both day and night?
Nine participants get the voices both day and night. A 10th participant answered that he receives his usually only very early in the morning around one o’clock. One target says that he no longer receives the voice.
- If the answer is both, are the voices clearer in the daytime or the nighttime?
Four participants stated that the voices are about the same always. One participant stated that the voices are clearest at his work place (daytime). One participant said that the voices range from “normal” to barely audible. One participant said that it seemed to be clearer about the time he wakes in the morning. An 8th participant stated that he usually gets the voices only very early in the morning. A 9th participant said that the voices are more audible at night. One participant failed to answer the question.
[The volume and clarity of the voices may depend on the targets’ environment.]
- Is there anything that seems to affect the clarity and volume of the voices?
Two participants stated “no.” One participant stated “the wind” increases the clarity and volume. Another participant stated “electric motors and other appliances.” Another participant answered that “noise-cancelling” ear sets dimmed the volume. One participant said that being deep underground (a cave) affected both the clarity and the volume (not audible). A 6th participant said that the way he “listened” affected the clarity and volume of the voices. The other 4 answers were unclear, which probably means that the question was not phrased correctly.
[It is probably only natural that the clarity and volume would vary in different ways among victims. Victims may not be consciously aware of some of the ways that affect the clarity and volume of the voices unless they keep detailed journals of their attacks.]
- Do the voices criticize you when you go about your daily tasks or are doing something that requires some deeper thought?
Nine participants answered “yes.” A 10th participant said “no.”
[Trying to make victims feel like failures or feel unworthy is a psychological ploy of the attackers. The attackers know that constant criticism is an effective means of psychological torture.]
- Do the voices threaten to do harm to you?
All 10 participants answered “yes.”
[Threatening harm is a psychological facet of the attack system, as it heightens anxiety in victims and causes victims to believe that death, accidents, etc. loom over them.]
- Do the voices threaten to do harm to family members and/or friends?
Nine participants answered “yes.” A 10th participant said “just me.”
[Threats to do harm to victims’ family members and friends are often more harmful to victims than threats against the victims themselves, for the victims feel that somehow they are responsible for those threats. This lends to inducing anxiety in victims, which is one of the main objectives of the attackers. If family members and friends know about the targeting, it can also strain relations between them and the target.]
- Do you talk back to or dialog with your attackers through the V2K?
Eight participants answered “yes.” One said “not often.” A 10th participant said that he tried not to (however, it appears that the participant’s thoughts went out to the attackers).
[Oftentimes target involuntarily communicate with the attackers. For example, the attackers often interrogate us through the voices. When they ask questions, the victims cannot help thinking the answers. That, of course, strongly suggests that the attackers do indeed read our thoughts.]
- Do you believe that the attackers can read your thoughts?
Eight participants were sure that they could. Two participants thought that perhaps the attackers first planted the thoughts and then acted as though they understood them.
[If a victim communicates by mental telepathy with the attackers (without using his voice), by definition the attackers are listening to his thoughts. Moreover, various patents prove that the attackers can read targets’ minds by remote. It may also be true that the attackers do indeed plants certain ideas and then proceed to pull those ideas from the targets minds. However, even if the latter is true, it also strongly suggests that the attackers can read thoughts.]
- Is there somebody or several people whom you know that the attackers often talk about?
Nine participants said “yes.” Only one stated “no.”
[This is very intentional on the part of the attackers, for they want the target to be aware that they know those people. Planting negative thoughts about friends and relatives and causing targets to be fearful for those friends and relatives are part of the attack scheme.]
- What do the attackers say about that person or those people?
Nine participants gave varying answers. One participant had answered “no.”
[All nine answers make it clear that the attackers want to create stress and anxiety in the victims.]
SET 4
- Do you feel that the V2K attackers sometimes blank out your thoughts?
Seven participants answered definitely “yes.” Three participants answered differently, but all three answers point to attackers being able to blank out thoughts.
[Blanking out thoughts appears to be a part of the attackers’ modus operandi. It is a way to convince targets to depend on the attackers, for after blanking out the thoughts, the attackers supply the answers.]
- Do you feel that the attackers sometimes cause certain thoughts to surface in your mind or tell you what to say?
Nine participants said “yes.” One said that they attempt to.
[It is clear that the attackers attempt to influence targets’ thought through planting negative ideas. This is a main facet of mind control.]
- Do you also receive physical torture along with the voices of the attackers?
Nine participants stated definitely “yes.” A 10th participant said “no,” but that he had been hit with directed energy weapons several times.
[It is clear that the attackers augment with voices with painful effects or vice versa. Obviously physical torture is a part of the plan to accompany the voices. The voices are much more effective when they are received along with the physical and neurological symptoms.]
- If the answer is yes, please describe those physical effects. Severe pain, shooting bone pain, kidney failure, facial paralysis, coma, malnutrition, nausea, vomiting, severe headaches, mutilation through virtual rape, cervical cancer, electronic harassment, ear pain, severely burning limbs or scalp, simulated sexual molestation, muscular spasms, severe cramps, severe joint pains in legs, arms and hands, choking spells, chest pains, teeth cracking, eardrum bleeding, painful vibrations, lower back pain, pings, electronic rape, burning, blistering, squeezing, stinging, being pushed, body heating, induced dreaming, complete takeover of all body systems (nervous, endocrine, hormonal, brain), pain infliction, temperature control, involuntary muscle movement, inability to breathe through my nose, electrical shocks, neurological takeover, burning, itching, sneezing, nose bleeding, bowel or urine incontinence, artificially regulated heart rate and blood pressure, skin and hair imbalances, visual disturbances, tremors, obnoxious odor coming from body, forced crying, excessive swallowing, nasal discharge, pain in the head, blurred vision, imbalance while walking, ankle and feet pain, face and back pains (causing it to be very stiff and painful), severe attacks on head, face burning, loss of eye to hand coordination, and attacks on shoulder (the top of it very painful). face, when I brush my teeth they make me lose my eye to hand coordination, they attack my left shoulder, the top of it making it hurt, muscle spasms, stinging, itching, burning, severe headaches, pains in lower back, and the back of the neck, skin tension, attacks on teeth, sexual assault, pains in the groin and pelvic and pubic areas, sleep deprivation, bruising, scratches, and pain to feet and legs.
[It is clear that the attackers have at their disposal an arsenal of physical effects that they can cause. The attackers appear to be free to choose from their arsenal of weaponry what physical and neurological effects to use on targets to achieve their aims.]
- Do the voices tell you and try to convince you that you are crazy?
Six participants answered “yes.” Only one participant stated “no.” An 8th participant said that they used to but now only rarely suggest it. A 9th participant said “sometimes.” The 10th participant answered the question in a different manner, making it difficult to determine his answer.
[The attackers obviously want the targets to think that they are crazy and they do everything they can to manipulate the targets to appear to be crazy to make them undergo “psychiatric evaluations.” That undermines a target’s credibility so that nobody, including law enforcement, believes them.]
- Do the attackers use any code words/expressions or “trigger” words/expressions?
Eight participants realized that their attackers used “trigger” words and expressions on them. One participant said “no, everything is repetitive.” Another participant said that he couldn’t think of any but was sure that the attackers used them.
[The attackers will almost invariably use certain “trigger” words and expressions for targets, words and expressions that affect the targets’ emotions in one way or another. Those triggers will be as varied as the targets and will be meaningful for those individual targets.]
- Do the attackers use obvious recordings along with their real time talking?
Seven participants answered “yes.” Two others received a form of recordings. One answered flatly “no.”
[Recordings appear to be a labor saving device used by the attackers. Those recordings and perhaps artificial intelligence help in filling in gaps between real-time talking. The use of recordings appears to be a regular part of the attack plan. Its use probably depends on the number of attackers in the group assigned to particular targets.]
- Along with the V2K, do the attackers sometimes manipulate your sexual organs?
In eight cases, the attackers tamper with targets’ sexual organs. Two participants answered “no.”
[The attackers appear to tamper with targets’ sexual organs perhaps to annoy the targets, to humiliate them with unwanted sensations, to achieve sleep deprivation, to instill in them a feeling of helplessness, or perhaps to program them into associating sex with other persons mentioned in their V2K.]
- Do the attackers attempt to connect you sexually with (anything taboo) through their V2K?
Eight participants answered “yes.” Two answered “no.”
[The attackers in most cases appear to use sex to instill guilt as one of their attack methods. Associating targets’ sexual thoughts with (anything taboo) frustrates targets and heightens anxiety in them. Because of the psychological sex association, targets often become (isolated).]
- Can you hear the voices when you are conversing with others, watching TV, on the phone, or otherwise distracted?
Eight participants said that they could still hear the attackers’ voices while talking with other people, watching TV, etc. One stated “no, not usually.” A 10th participant did not answer that question.
[This indicates that the voices are continuous, which also suggests that they do indeed use recordings during the V2K that continue regardless of what the targets are doing.]
SET 5
- Have the attackers ever spoken to you in other languages?
Seven participants answered “no.” Only three answered “yes.”
[Most Americans are monolingual. Thus, in general, the attackers use only the language known to the targets. In all three cases of participants who answered “yes,” other languages were probably meaningful to them for various reasons. The use of other languages aid the attackers in hiding their true identities. It is highly likely that the languages used are recorded and that the attackers themselves do not know those languages.]
- If so, does that language or those languages have any particular significance in your life?
Please see the answers to Number 1.
- Do the attackers ever ask you about your “relationship” with a particular individual or group?
Six participants answered “no.” Several said that they answered “no” because the attackers already knew about those relationships. Four answered “yes.”
[Much of V2K appears to involve interrogation and interrogation techniques. There are patented devices and methods that compel the victims to answer questions truthfully. This suggests that targets are objects of various types of experimentation.]
- Have you experienced a ringing in the ears (tinnitus) ever since you first heard the voices?
Nine participants answered “yes.” A 10th participant heard sounds that he tried to explain: “Yes, I hear noises from it [but it] is not from tinnitus. I am attacked with a DEW and the directed energy ‘washes’ down the sides of my head.”
[Tinnitus occurs in almost all cases where targets hear voices. It is not yet known whether the tinnitus is caused intentionally by the attackers only to annoy the victims or whether it is an effect of the device used on the targets. More study of tinnitus should be conducted to determine the cause.]
- Do the voices ever seem to come from the shower head or the spewing water when you shower?
Seven participants answered “yes.” One said that at first they did but no longer do so. Two answered “no.”
[That the voices seem to come over the water when showering strongly suggests the attackers’ use of remote directed sound. As in the case of tinnitus, it is still not known whether this is intentional on the part of the attackers or simply a pervasive effect of the method or device for projecting the voices.]
- Do you attackers especially bother you the night before an important event (a job interview, departure for a trip, etc.)?
Nine participants answered “yes.” Only one answered “no.”
[Sleep deprivation is a major tactic used by the attackers. The objective is to affect the alacrity of the victims the following day, cause them to oversleep the next morning for their appointments or in carrying out their plans, and induce anxiety.]
- Do you sometimes wake at night with the attackers showing you photos of people, places, or objects and interrogating you about them?
Seven participants answered “yes.” Two participants answered that they were shown pictures, holograms, etc. but were not necessarily questioned about them. One participant answered “no.”
[It is clear that the attackers have the capability to project images into a target’s mind just as they have the capability of projecting the voices to his head.]
- Do the attackers pretend that their intention is to extort money from you or blackmail you and yet do not follow up on it in their actions?
Four participants said that the attackers had indeed stolen money from them or caused them to lose money in one way or another. Only two participants answered “no.” One participant said that they threatened identity theft and talked about extorting money from others. One participant answered “not really” but they practiced workplace mobbing and blacklisted him. Another participant said that from the beginning it was about money and extortion but later they offered him money to join them. One answer could not be interpreted.
[If the attackers do indeed steal money from targets, I suspect that the main reason is to fool targets into thinking that is their purpose.]
- Do the attackers ever ask you about places where you have lived or visited?
Three participants answered “no.” Four stated “yes.” Three participants stated that the attackers told them, not asked them, for they already knew about those places.
[That the attackers already know those places suggest that they know the targets, have researched the lives of the targets, and have mined the thoughts of the targets. I suspect that in the case where targets are asked about those places, the attackers are attempting to force them to tell them to tell the truth or seeing whether the targets are lying.]
- Have the attackers ever told you or suggested to you why you were selected for targeting?
Eight participants were told various reasons why they were selected. Only two participants stated that they had never been offered an explanation.
[The attackers appear to attempt to delude the victims about why they were selected for targeting. The attackers are not likely truthful in any case, for if they were, the victims would know where to concentrate their research about the identities of the attackers.]
- Do the attackers use local words and expression in common usage in your area?
Six participants answered “yes.” One participant said “sometimes.” Only two stated “no.” One participant did not answer the question.
[Regardless of who or what organization might be behind victims’ targeting, they appear to select attackers who either live in the same area of the victims or who know the area and the vernacular well.]
Do the attackers ever tell you something specific to do or not to do?
Nine participants answered “yes.” Only one stated “no.”
[The answers suggest that the attackers either practice a form of “behavior modification” or wish to exercise control over targets. In both cases, in my opinion, it hints of experimentation.]
- Do the attackers ever suggest to you that you have a disease, a pain, or a condition?
Eight participants answered “yes.” One participant stated “no.” A 10th participant said that he did have several diseases but that the attackers tried to convince him that he was only lazy.
[Attackers often use the power of suggestion to make targets believe that they have certain ailments. There is even evidence that the attackers can actually cause those ailments through the continual power of suggestion, usually through inaudible voices to the subconscious that the targets do not hear.]
- Have the attackers ever asked you or suggested to you that you join them?
Six participants stated “no.” Four persons answered “yes.”
[Occasionally the attackers will deceive targets into believing that the attackers want targets to join them. In my opinion, that is total deception. If that were true, somebody would probably contact the targets directly in some manner without first torturing them.]
- Do the attackers ever urge you to commit suicide?
Eight participants answered “yes.” One participant answered that they had in the past but not lately. Only one person stated “no.”
[The attackers’ attempt to make targets commit suicide is very commonplace, for suicide is a sure way to neutralize the targets. Their urging targets to do so may also be part of an experiment in subliminal suggestion. Constant sleep deprivation, social isolation, and continual physical and neurological torture do cause some targets to end their lives.]
- Do the attackers ever tell you something that people say or think about you?
Eight participant stated “yes.” Only one said “no.” A 10th participant said that they only repeated topics of conversations that he had had with others that day.
[One of the aims of the attackers is to isolate targets socially. Telling targets lies (or perhaps even truths) about what people say about them strains targets’ relations with those people, thus lending to isolation.]
[Attackers try hard to cause problems for targets and get them jailed or sent for “psychiatric evaluation.” Once they are either jailed or mentally evaluated, they are no longer credible.]
- Do the attackers pretend that they can see you?
Nine participants answered “yes.” A 10th participant said “not anymore, but I know they can see my exact location somehow and probably my thermal image.”
[There are various inventions that allow people to view others by remote. All of the participants seem to be convinced that their attackers can actually see them or at least be able to locate them anywhere.]
- Do the attackers ever pretend to be concerned for your safety, for example, telling you not to overwork in the heat, that you have a low tire on your car, or warning you not to go upon a ladder?
Six participants answered yes for various reasons. Three said “no.” A 10th participant stated “kind of.”
[The attackers try to gain the confidence of targets to exercise control over them. One way to do so is to pretend to give helpful advice. It is simply a ploy and is not at all sincere.]
Do the attackers ever mention places on your body that are not readily visible to other people, e. g., a hidden tattoo, a scar, or a birthmark?
Five participants answered “yes.” Four answered “no.” Another participant did not answer the question.
[The attackers want targets to believe that the attackers know even the most intimate details about them. This makes targets feel vulnerable and violated, thus contributing to anxiety.]
End of 2017 Study Thank you TI study!

The 2018 Survey
Eleanor White, an auditory target who receives only occasional V2K, conducted a survey of auditory targets in the summer of 2018. Eighteen auditory targets completed the survey. Their answers are calculated in percentages. That survey follows.
Please check ONLY ONE of the following two choices:
0% My voice to skull transmissions are only ONE WAY, from the attackers to me.
100% My voice to skull transmissions are TWO WAY, and the attackers can also receive my voice.
Please check ONLY ONE of the following two choices:
61% My voice to skull transmissions are continuous, 24/7 or nearly so.
39% My voice to skull transmissions are sporadic.
These choices apply to what I HEAR FROM the attackers:
83% I hear plainly audible voices within my skull.
17% I hear plainly audible voices within other body parts.
72% I receive odd sounds, beeps, tones, clicks, buzzes within my skull intermittently.
50% I receive a nearly constant tone within my skull that seems artificial (not natural tinnitus).
11% I receive odd sounds, beeps, tones, clicks, buzzes within other body parts.
78% I receive essentially silent “injected thoughts.”
78% My attackers give me commands by voice to skull.
78% My attackers insult me by voice to skull.
72% My attackers threaten me by voice to skull.
56% My attackers urge me to harm myself or others by voice to skull.
72% My attackers lecture me on alleged personal faults by voice to skull.
50% My attackers disparage family and associates by voice to skull.
39% My attackers send voices that sound exactly like family or associates by voice to skull.
22% My attackers send a voice that sounds like my own voice by voice to skull.
50% My attackers send voices that appear to be unintentional (“open mic”) conversations among the attackers themselves by voice to skull.
* Physical sensations other than sound are outside the scope of this survey. Attacker-caused sounds that originate away from the skull or body are also outside the scope of this survey.
These choices apply to what the attackers RECEIVE FROM ME:
78% My attackers say things that show that they hear what I am thinking.
72% My attackers say things that show that they see what I am seeing.
67% My attackers say things that show that they sense what I am feeling.
78% My attackers say things that show that they see what I am physically doing.
72% My attackers set up harassment scenarios showing they know what I had planned.
Countermeasures against the Voices:
28% I have a successful countermeasure against voice to skull.
0% My countermeasure is totally successful.
17% My countermeasure is partially successful.
0% My countermeasure success is permanent.
17% My countermeasure success is temporary.
End of 2018 Survey
A Possible User Manual
Similarities in the tactics used by the attackers suggest that they all made use of a type of user manual in performing the assaults on their victims or were trained by someone who had had access to the manual. Such a manual, to the knowledge of current targets, has not been explicitly published unless it has been so highly classified that it has not yet been leaked. The assault activities of the manual do not easily subscribe to chronological order or sequences. Some of the activities follow upon others, and some of them occur concurrently with one of more other activities.
Based on known government programs using similar methods, such as MKUltra and COINTELPRO, the plan of attack shows that the development of the manual probably received input from the medical community, particularly psychiatrists and psychologists, from the intelligence community, from law enforcement, from various categories of scientists, from research institutions, and from other entities. The attack plan appears to require the following steps: (1) Identify the targets and research their backgrounds. (2) Determine what form of targeting can best neutralize the targets. (3) Select the appropriate attackers for the targets. (4) Execute the attacks.
After the first three steps have been achieved, the attackers begin their operations in executing the plan. Activities of the plan include (1) isolating the targets from relatives, friends, and the community, (2) causing the targets to act in such a manner that they appear mentally unstable, (3) encouraging targets to commit suicide. (4) causing targets to react to their targeting in ways that get them incarcerated or committed to mental institutions. (5) damaging targets’ credibility so that nobody will believe their complaints. (6) making their lives unbearable. (7) and many other activities whose purpose is to neutralize the targets.
It seems safe to assume that of the hundreds of persons involved in developing the manual, some participants had their own agendas. Thus, various other groups over the ensuing decades probably gained access to the content of the manual and to the devices, methods, and knowledge for carrying out the targeting effects. Studies of V2K have found ample reason to believe that targeting is not carried out by a single organization but probably by several or perhaps many organizations.
The Possible Perpetrators or Attackers
Although we cannot state with absolute certainty what organizations today might have the desire and the capability to use V2K as a weapon, we can narrow down the possibilities by examining several logical requirements for its wide usage. The entity will probably have (1) substantial financial resources to produce or procure equipment used for that operation and also to maintain and distribute it, (2) a principal headquarters and considerable infrastructure for its operations, (3) well equipped research facilities, (4) a large cadre of operator personnel at its disposal, (4) the means or the authority to command a high degree of secrecy concerning its usage, and (4) highly secret training facilities, probably in more than one city or area.
Remote-delivered electronic assault, including the V2K, is probably expensive. Thus, we have to ask ourselves, “Why go to the time, trouble, and expense of attacking someone using that means? Reasoning leads us to two principal reasons: (1) To exact revenge upon and punish their perceived enemies. Those enemies might be whistleblowers, political, civil rights, and environmental activists, in some cases perhaps individuals for personal reasons, and others. (2) To conduct illegal experiments on targets chosen either deliberately or at random.
It is a widely known fact that US Government entities have engaged in illegal experimentation on American targets on American soil for many years. Wikipedia states that those experiments included “exposure of people to many chemical and biological weapons (including infection of people with deadly or debilitating diseases), human radiation experiments, injection of people with toxic and radioactive chemicals, surgical experiments like KX-338, interrogation and torture experiments, tests involving mind-altering substances, and a wide variety of others.”
Possible Experiments Concerning the Voices
In as much as animals do not have the power of speech or the ability to understand most of human speech, experiments dealing with the remote-delivered voices must necessarily be carried out on humans. We have not been able to discover any common human characteristics that the attackers seek in experimental auditory targets. Indeed, victims may simply be opportunity targets selected at random, and some of them may be targets chosen primarily for punitive reasons.
Remotely delivered voices transmitted to auditory targets who are the only ones to hear those voices are obviously tools for mind control, the expected result of neurological warfare. Many results of those transmissions are probably no longer experimental but are long proven to be effective. The following examples represent some of the possibly proven and ongoing experiments that we believe the attackers have conducted in perfecting mind control techniques.
We believe that the following experiments probably seek to determine whether auditory targets:
(1) can be driven to insanity by the voices.
(2) can be made to commit illegal acts, including murder.
(3) can be made to be disloyal to their governments and engage in sabotage and espionage.
(4) can be persuaded to commit suicide.
(5) will respond to certain embedded codes and hypnotic triggers.
(6) will subscribe to a particular doctrine or a belief due to propaganda carried by the subliminal voices.
(7) can be made to relocate or travel to places designated by the attackers.
(8) can be taught the capability of hearing inaudible voices and sounds.
(9) can be taught to solve difficult situations and puzzles.
(10) can be made to stop some particular activity.
(11) contrarily, can be made to engage in some particular activity.
(12) can be persuaded to identify sexually with the opposite gender or the same gender.
(13) might be made to hate a particular group or cease to hate a particular group of people.
(14) can be made to endure the most excruciating torture.
(15) can be made to inform on friends, family members, and others who are committing crimes or treason.
(16) can be made to memorize certain codes and other information without realizing it.
(17) and can be made to respond to many other mind control effects.
Neurological warfare is real. The US and other countries have zealously pursued neurological warfare for decades as the next frontier in subjugation methods. The research conducted in those efforts is without a doubt far ahead of mainstream scientific and public knowledge. We believe that illicit human experimentation will continue and will probably increase in the numbers of victims used in the experiments.
Institutions and Neurological Experimentation
Many universities and institutions carry out neurological experimentation on their own for various reasons, and others perform the experimentation under contracts with the US Government for specific uses. For example, eighty institutions participated in the government’s MKUltra mind control program in the 1950s and 1960s. Most of the universities involved in the program claim that they were not aware that their contributions would be used for neurological warfare.
Government agencies alone cannot conduct all of the necessary experimentation; thus, they must depend on individual inventors, research institutions, public and private laboratories, universities, public entities, and sometimes big businesses for providing research for the objectives sought. Those sources naturally welcome the large grants given them for those experimental studies.
We can only surmise that the institutions’ neurological studies include areas related to V2K. Many institutions engage in studies concerning schizophrenia. As auditory targets are normally considered schizophrenic, those institutions must necessarily be aware of the voices and may very well be studying certain aspects of the voices. Whether some of the institutions actually employ the devices and methods used in transmitting the voices had not yet been answered.
A few of the institutions that perform research on schizophrenia follow.
— Stanford
— National Institute of Health (NIH)
— Harvard University
— National Institute of Neurological Disorders and Stroke
— National Institute of Mental Health
— Barrow Neurological Institute
— Mischer Neuroscience Institute
— Johns Hopkins University
— Yale School of Medicine
— Lawson Health Research Institute
— Stanley Medical Research Institute
Guidelines for Experimentation
The US Government and some states, as well as various institutions and organizations have in recent years spelled out certain guidelines for ethics in conducting experiments.
The Department of Health and Human Services is mandated with determining the guidelines for human experimentation in the United States. Those guidelines may be seen in the department’s official web site. Although the policy is meticulously laid out, there are provisions that might exempt particular experiments.
For example, Article 46.101 (c) states that “Department or agency heads retain final judgement [sic] as to whether a particular activity is covered by this policy.” In Section (i) “. . . department or agency heads may waive the applicability of some or all of the provisions of this policy to specific research activities or classes of research activities otherwise covered by this policy.” Thus, that leaves ample room for allowing illicit experiments on auditory and other targets.
The American Psychological Association (APA) also outlines elaborately its rules of ethics in conducting research. According to Deborah Smith’s January 2003 article “Five Principles for Research Ethics”–she actually lists seven–concerning the American Psychological Association Science Directorate, the APA requires researchers to advise research participants as quoted below.
The purpose of the research, expected duration and procedures.
- Participants’ rights to decline to participate and to withdraw from the research once it has started, as well as the anticipated consequences of doing so.
- Reasonably foreseeable factors that may influence their willingness to participate, such as potential risks, discomfort or adverse effects.
- Any prospective research benefits.
- Limits of confidentiality, such as data coding, disposal, sharing and archiving, and when confidentiality must be broken.
- Incentives for participation.
- Who participants can contact with questions.
Based on the nature of their targeting, many auditory targets and other targets insist that they are subjects for experimental programs. In no case concerning auditory targets and other targets has the person willingly and knowingly volunteered for an experiment. Experiments that involve neurological warfare require the participation of human subjects. In some cases, the results are obviously more revealing if the subjects do not know that they are experimental subjects.
Remote Neural Monitoring (RNM)
The origin of this term is unknown. Many targets, including some auditory targets, believe that they receive remote neural monitoring (RNM), an attack that includes many of the physical and neurological effects of targeting, including the voices. That hints that those targets who use the term remote neural monitoring to describe their targeting blame all of their effects on delivery by a single attack device and perhaps even by one single attack group. If such a method as RNM exists, its devices and methods are unknown and the program is currently classified technology.
RNM advocates thus appear to combine what we in this study differentiate as physical effects and neurological, or psychological effects. Here are some capabilities of the attackers attributed to RNM: (1) Tracking the victim. (2) Reading the victim’s mind. (3) Striking the victim with all types of physical effects. (4) Seeing through the victim’s eyes. (5) Hearing what the victim hears. (6) Projecting voices into the victim’s head. (7) Tampering with appliances and devices in the victim’s domicile. (8) Causing tinnitus in the victim’s head. (9) Injecting commands into the victim’s mind. (10) Conducting organized stalking against the victim. (11) And other capabilities.
Mind Reading and V2K
In all three of the V2K studies, most of the auditory targets are convinced that their attackers can read their minds. Whenever the attackers can hear a person’s thoughts, even slightly ahead of the completion of those thoughts, and then reply to a person’s specific thoughts, it means that they have the capability to mind read. Call that process “telepathic translations” or whatever, but it is the very definition of mindreading.
Although scientists have worked for decades on mapping the brain, the public is led to believe that their efforts are far from complete. Millions of brain cells and nerves remain to be identified and studied for their functions. Nevertheless, scientists have apparently been successful in discovering the functions of many of the brain’s locations. Knowing those functions, scientists have learned to utilize them for both helpful and harmful purposes.
Some of the harmful functions used on targets include the ability to use the brain for inserting holographic images in people’s minds, inducing dreams and manipulating them, seeing what the target sees, create scenarios portraying the past experiences of the target, and other functions. Most targets believe that it is obvious that scientists have learned to delve into the thoughts of people’s brains and read those thoughts. Indeed, if the attackers comment on the auditory targets’ thoughts, it is only logical that the attackers somehow know what those targets are thinking. That means that the attackers can read the minds with one or more of the devices at their disposal.
Skeptics believe that mind reading is impossible. That idea has been largely refuted by the increasing number of patents relating to that topic. The BBC on May 7, 2015 discussed the recent dramatic increases in patents related to “reading brainwaves.” It stated that in the US from 2000 to 2009 fewer than 400 patents concerning neuro-technology were filed. However, in 2010 that number doubled, and in 2014 alone 1,600 similar patents were submitted to the Patent Office. Keep in mind that European countries are also issuing similar patents.
As in the case of inventions concerning the voices, out of the many inventions, at least a few have undoubtedly been successfully demonstrated. Many of the patents refer to the use of EEG signals in the process of mind reading.
The Science Daily reported on February 22, 2018 that neuroscientists at the University of Toronto Scarborough have developed a method to use mind reading algorithms with EEG data to view images of what people see. One of the scientists involved in the experiment stated, “What’s really exciting is that we’re not reconstructing squares and triangles but actual images of a person’s face, and that involves a lot of fine-grained visual detail.”
Targets have often questioned whether the attackers hear their thoughts using headphones or whether they read the thoughts from a monitor. The statement by the Toronto scientist above states that scientists can see the faces, which means that they would be seen on a screen or a monitor. Chandra Steele in a June 19, 2015 article in PCMag also writes that, “Scientists have made some startling breakthroughs in reproducing our thoughts on a screen and delving into what motivates us to do the things we do.”
However, many other questions concerning mind reading still remain to be answered. For example, we do not yet know the various devices used in the process of mind reading nor how they make the initial contact with the subjects. We also do not know whether the device that gives attackers the capability of reading minds is the same device used to transmit the voices.
Despite those unanswered questions, according to statements of longtime auditory targets, their attackers have had a finely tuned, highly accurate mind reading device for at least two decades. Mindreading and V2K go hand in hand in accomplishing mind control. Most targets are acutely aware that the US Government and those of other countries discover neurological breakthroughs many years before that knowledge becomes public.
“Conclusions –This study makes the case that two activities of targeting disbelieved by most of the public and ridiculed in the media and by law enforcement not only take place but also are proliferating at an alarming degree: (1) the transmission of voices by remote to auditory targets, who are the only ones to hear those voices, and (2) the reading of minds by remote methods. It also shows that the attackers use similar tactics in employing the voices.” – Thank you to the “Auditory Targets: A study of Synthetic Telepathy, or V2K, An Aspect of Electronic Targeting (October, 2018)”
 Curled leaf
Curled leaf
Thank you sweet God for everything exactly the way it is today. Thank you dear God for bringing the Network Collective into the light for justice and bringing the Network Collective down God to conquer them. Thank you dear God for protecting, loving and guiding family, friends, territories, tools, vehicles, our animals, plants and me. I love you God. I thank you God. So be it. It is so. Amen.


 On Nov. 23, 2018- danger magnetic 5, set on 0-3 range. Up against running furnace in friends apartment in St. Louis, MO …
On Nov. 23, 2018- danger magnetic 5, set on 0-3 range. Up against running furnace in friends apartment in St. Louis, MO … But the dangerous Magnetic 7, set on 0-3 range two points higher is registered at my friend’s dining room table. Those ‘neighbors’ using the directed microwave, radio wave, magnetic wave weapons knew from through-wall-radar that I took photos of EMF readings… because next day all levels were reduced.
But the dangerous Magnetic 7, set on 0-3 range two points higher is registered at my friend’s dining room table. Those ‘neighbors’ using the directed microwave, radio wave, magnetic wave weapons knew from through-wall-radar that I took photos of EMF readings… because next day all levels were reduced. Next day, Magnetic 6 at same table.
Next day, Magnetic 6 at same table. Magnetic 6 on door knob facing hall Nov. 23, 2018.
Magnetic 6 on door knob facing hall Nov. 23, 2018. Next day magnetic 4.5 same door knob.
Next day magnetic 4.5 same door knob. Magnetic 7 on 0-3 range on dining room chair Nov. 23, 2018.
Magnetic 7 on 0-3 range on dining room chair Nov. 23, 2018. Next day magnetic 5 on same chair.
Next day magnetic 5 on same chair. Magnetic 7 against wall on back of sofa Nov. 23, 2018.
Magnetic 7 against wall on back of sofa Nov. 23, 2018. Next day magnetic 5 on back of same sofa against wall. -FYI the towers on computers at the Springfield, MO Library Center register magnetic 1.5 in comparison.
Next day magnetic 5 on back of same sofa against wall. -FYI the towers on computers at the Springfield, MO Library Center register magnetic 1.5 in comparison. Chemtrails above public gardens. When friends and I left a garden dome to walk outside on a lovely day, a helicopter (from Mississippi River tourist-pad) did two flyovers, circling repeatedly in broad daylight above where we walked:
Chemtrails above public gardens. When friends and I left a garden dome to walk outside on a lovely day, a helicopter (from Mississippi River tourist-pad) did two flyovers, circling repeatedly in broad daylight above where we walked:
 Flew off.
Flew off.  Back again.
Back again. Then finally flew away.
Then finally flew away.


 In St. Louis, MO endured non-stop directed microwave weapons attacks (it was thirty degrees outside and had to completely open a guest bedroom window from heat, though friend keeps apartment cool.) The directed microwave weapons attacks were specifically centered on lower stomach, causing extreme pain in organs there- for three days. (Interestingly when visiting another friend in a southern state, the targeting is only on my skull. After visiting with him, cannot finish sentences or remember words, due to concussive injuries to brain. -Just like the brain concussions suffered in what our government State Department officials term ‘health attacks’ from directed microwave, radio wave and acoustic weapons used against U.S. Cuban and Chinese diplomats.) It takes over a month to recover.
In St. Louis, MO endured non-stop directed microwave weapons attacks (it was thirty degrees outside and had to completely open a guest bedroom window from heat, though friend keeps apartment cool.) The directed microwave weapons attacks were specifically centered on lower stomach, causing extreme pain in organs there- for three days. (Interestingly when visiting another friend in a southern state, the targeting is only on my skull. After visiting with him, cannot finish sentences or remember words, due to concussive injuries to brain. -Just like the brain concussions suffered in what our government State Department officials term ‘health attacks’ from directed microwave, radio wave and acoustic weapons used against U.S. Cuban and Chinese diplomats.) It takes over a month to recover. At Lone Elk Park outside St. Louis, MO.
At Lone Elk Park outside St. Louis, MO.




 Radio personality Tommy Nerd.
Radio personality Tommy Nerd.


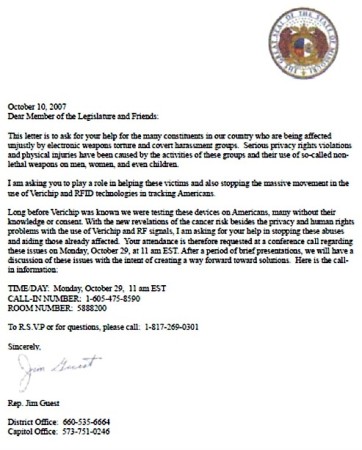

 Photographed dog’s spirit.
Photographed dog’s spirit.











 Letter left on front porch of TIs home after attempts to murder their dog failed.
Letter left on front porch of TIs home after attempts to murder their dog failed.
 Curled leaf
Curled leaf God’s beauty.
God’s beauty.
 Some targeted individuals have the ability to take photos of psychic phenomenon.
Some targeted individuals have the ability to take photos of psychic phenomenon. David Remnick wrote for the Washington Post: “The experiments of 1957-1961 were done on patients, mostly women, who entered the Allan Institute voluntarily, usually at the recommendation of a private physician.” “Cameron was part of an international committee of psychiatrists and social scientists… published numerous articles… Cameron began the Allan Memorial Institute in 1943 with the help of a grant from the Rockefeller Foundation.”
David Remnick wrote for the Washington Post: “The experiments of 1957-1961 were done on patients, mostly women, who entered the Allan Institute voluntarily, usually at the recommendation of a private physician.” “Cameron was part of an international committee of psychiatrists and social scientists… published numerous articles… Cameron began the Allan Memorial Institute in 1943 with the help of a grant from the Rockefeller Foundation.”
 2GC-660 MO… Do these trucks belong to same man?
2GC-660 MO… Do these trucks belong to same man? A salute to anyone smiling a toothy grimace at any security camera anywhere; but most especially when they are being targeted right then and there with directed energy weapons… because all the SECURITY in the world cannot see DEWs locked onto TIs and streamed into them, in public institutions, churches, parks or elsewhere.
A salute to anyone smiling a toothy grimace at any security camera anywhere; but most especially when they are being targeted right then and there with directed energy weapons… because all the SECURITY in the world cannot see DEWs locked onto TIs and streamed into them, in public institutions, churches, parks or elsewhere. One store’s security car on So. Campbell Ave. in Springfield, MO.
One store’s security car on So. Campbell Ave. in Springfield, MO. Ten cameras visible at this one entrance, not including those directly over entrance doors with government facial recognition software.
Ten cameras visible at this one entrance, not including those directly over entrance doors with government facial recognition software.
 Three more cameras over a giant store sign at same location. Did not count the cameras or take pictures of those over the second entrance or garden entrance. Springfield, MO police evident during this photo session and shopping expedition that lasted ten minutes. Below more on same parking lot:
Three more cameras over a giant store sign at same location. Did not count the cameras or take pictures of those over the second entrance or garden entrance. Springfield, MO police evident during this photo session and shopping expedition that lasted ten minutes. Below more on same parking lot:
 In the parking lot of same So. Campbell Ave. Springfield, MO store there are two Air Force ‘Live Eye’ poles with two cameras atop each that have government facial recognition software, and other surveillance devices on them. These stores are all government subsidized, and they use military style surveillance systems. This store’s ‘security’ is the forerunner of things to come in a few years all over America. Security companies main goal today is to watch and acquire data on ALL citizens… not just criminals.
In the parking lot of same So. Campbell Ave. Springfield, MO store there are two Air Force ‘Live Eye’ poles with two cameras atop each that have government facial recognition software, and other surveillance devices on them. These stores are all government subsidized, and they use military style surveillance systems. This store’s ‘security’ is the forerunner of things to come in a few years all over America. Security companies main goal today is to watch and acquire data on ALL citizens… not just criminals. God’s creation covering up for the winter.
God’s creation covering up for the winter.


 1509PD
1509PD
 In the US Naval Institute website January 31, 2018 a Lockhead EP-3E Aries II aircraft was ‘buzzed‘ by Russian SU-27 fighter to within five feet in the air over the Black Sea. From the Navy Air Systems Command website the EP-3E Aries II: t
In the US Naval Institute website January 31, 2018 a Lockhead EP-3E Aries II aircraft was ‘buzzed‘ by Russian SU-27 fighter to within five feet in the air over the Black Sea. From the Navy Air Systems Command website the EP-3E Aries II: t My country’s flag.
My country’s flag. In my home.
In my home.
You must be logged in to post a comment.